8 Best Practices to Prevent SQL Injection Attacks
- April 15, 2021
- < 1 min read
SQL injection is one of the most dangerous vulnerabilities for online applications. It occurs when a user adds untrusted data to a database query. For instance, when filling in a web form. If SQL injection is possible, smart attackers can create user input to steal valuable data, bypass authentication, or corrupt the records in your database.
There are different types of SQL injection attacks, but in general, they all have a similar cause. The untrusted data that the user enters is concatenated with the query string. Therefore the user’s input can alter the query’s original intent.
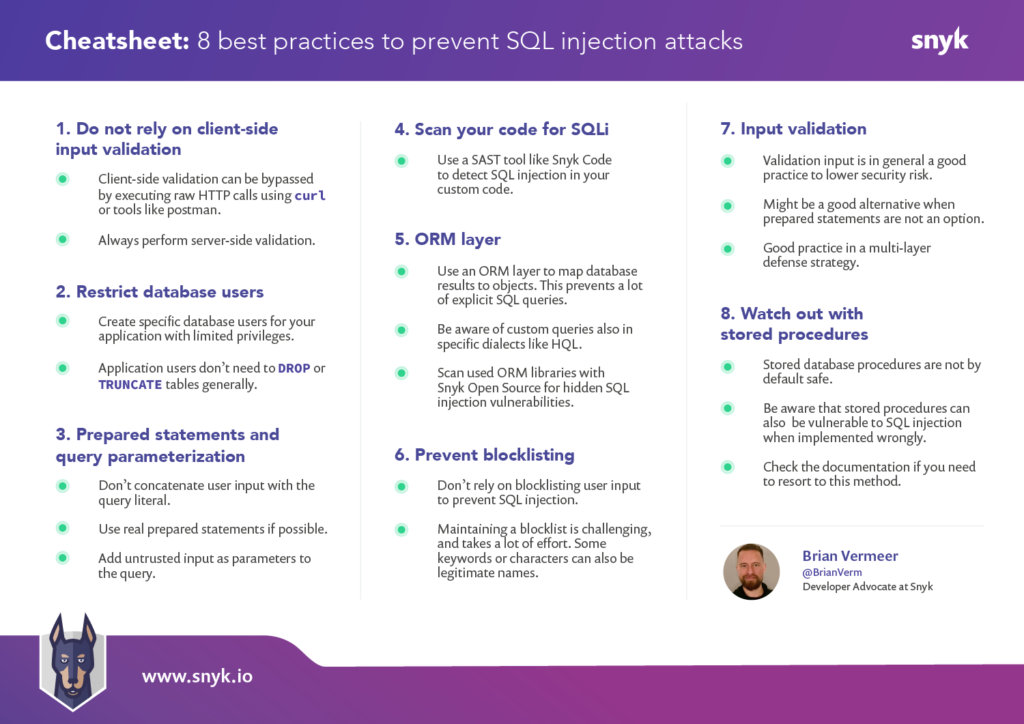
These are the 8 best practices we discuss in this article.
- Do not rely on client-side input validation
- Use a database user with restricted privileges
- Use prepared statements and query parameterization
- Scan your code for SQL injection vulnerabilities
- Use an ORM layer
- Don’t rely on blocklisting
- Perform input validation
- Be careful with stored procedures
- April 15, 2021
- < 1 min read





Comments (0)
No comments yet. Be the first.